Network Penetration Testing: Internal vs External with Real-World Use Cases
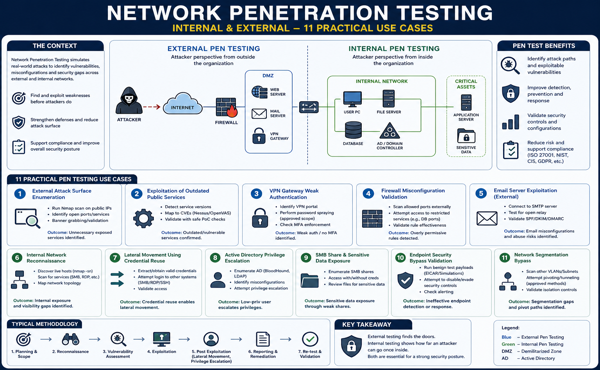
Network Penetration Testing (Pentesting) is a controlled and authorized simulation of cyberattacks to evaluate the security posture of an organization’s infrastructure. It helps identify vulnerabilities before adversaries exploit them and supports compliance frameworks like ISO/IEC 27001, ISO/IEC 17025, GDPR, and HIPAA.
Pentesting is broadly categorized into:
- External Penetration Testing – Simulates attacks from outside the organization (internet-facing assets).
- Internal Penetration Testing – Simulates insider threats or attackers who have gained initial access.
A mature security program requires both perspectives to effectively validate defense-in-depth strategies.
External Network Penetration Testing
Objective
To assess publicly exposed systems such as:
- Web servers
- VPN gateways
- Firewalls
- Email servers
- Public IP ranges
Key Focus Areas
- Attack surface discovery
- Exploitation of exposed services
- Misconfigurations in perimeter defenses
- Credential exposure
Internal Network Penetration Testing
Objective
To simulate an attacker inside the network (e.g., compromised endpoint, malicious insider) and evaluate:
- Lateral movement
- Privilege escalation
- Access to critical systems
Key Focus Areas
- Active Directory weaknesses
- Weak internal segmentation
- Credential reuse
- Sensitive data access
Some Practical Penetration Testing Use Cases
- External Attack Surface Enumeration
Scenario: Organization exposes multiple services (HTTP, HTTPS, SSH).
Test: Perform reconnaissance and port scanning to identify open services.
Outcome: Detect unnecessary exposed services and reduce attack surface.
- Exploitation of Outdated Public Services
Scenario: Public-facing server running outdated software.
Test: Identify known vulnerabilities (e.g., CVEs) and attempt exploitation.
Outcome: Demonstrates risk of unpatched systems and supports patch management controls.
- VPN Gateway Weak Authentication
Scenario: VPN portal exposed to internet.
Test: Password spraying or MFA bypass attempts.
Outcome: Identifies weak authentication controls and lack of brute-force protection.
- Firewall Misconfiguration Validation
Scenario: Perimeter firewall rules are overly permissive.
Test: Attempt access to restricted ports/services.
Outcome: Validates segmentation and rule hardening effectiveness.
- Email Server Exploitation (External)
Scenario: Misconfigured SMTP server.
Test: Open relay or spoofing tests.
Outcome: Prevents phishing abuse and reputational damage.
- Internal Network Reconnaissance
Scenario: Attacker gains access to one workstation.
Test: Scan internal network for live hosts and services.
Outcome: Identifies visibility gaps and unnecessary internal exposure.
- Lateral Movement Using Credential Reuse
Scenario: Same credentials used across multiple systems.
Test: Use harvested credentials to access other systems.
Outcome: Highlights need for strong identity and access management.
- Active Directory Privilege Escalation
Scenario: Misconfigured AD permissions.
Test: Exploit Kerberos/LDAP misconfigurations to escalate privileges.
Outcome: Demonstrates domain compromise risk.
- SMB Share and Sensitive Data Exposure
Scenario: Open or poorly secured shared folders.
Test: Enumerate and access SMB shares.
Outcome: Identifies data leakage risks and weak access controls.
- Endpoint Security Bypass
Scenario: Endpoint protection deployed but not hardened.
Test: Attempt to disable or bypass security controls.
Outcome: Validates effectiveness of EDR/AV solutions.
- Network Segmentation Bypass
Scenario: Critical systems expected to be isolated.
Test: Attempt pivoting across VLANs/subnets.
Outcome: Identifies segmentation gaps and improper access control.
Best Practices for Effective Network Pentesting
- Define Scope Clearly – Include IP ranges, systems, and exclusions
- Align with Frameworks – Map findings to controls (ISO 27001, NIST, CIS)
- Use Realistic Attack Scenarios – Simulate actual threat actors
- Prioritize Findings by Risk – Combine CVSS with business impact
- Validate Remediation – Conduct re-testing after fixes
- Integrate with SOC & DLP – Ensure alerts are triggered and monitored
Conclusion
Internal and External Network Penetration Testing together provide a comprehensive view of an organization’s security posture. While external testing helps reduce exposure to internet-based threats, internal testing reveals how far an attacker can move once inside.
Organizations that continuously test, validate, and improve their defenses are significantly better positioned to withstand modern cyber threats.
Author
-

Krishna Prasad is the Quality Manager at NABL IT Security’s ISO 17025-certified Security Testing Lab. He ensures that all security testing processes adhere to the highest quality standards and comply with global security regulations. With extensive experience in quality assurance, Krishna oversees the implementation of rigorous testing methodologies, guaranteeing that security assessments are both accurate and reliable.
Additionally, he manages asset tracking within the lab, ensuring that all security assets are effectively maintained, optimized, and up-to-date to support high-quality testing services. His dedication to quality and precision helps organizations enhance their security posture and meet compliance requirements in an increasingly complex cybersecurity landscape.