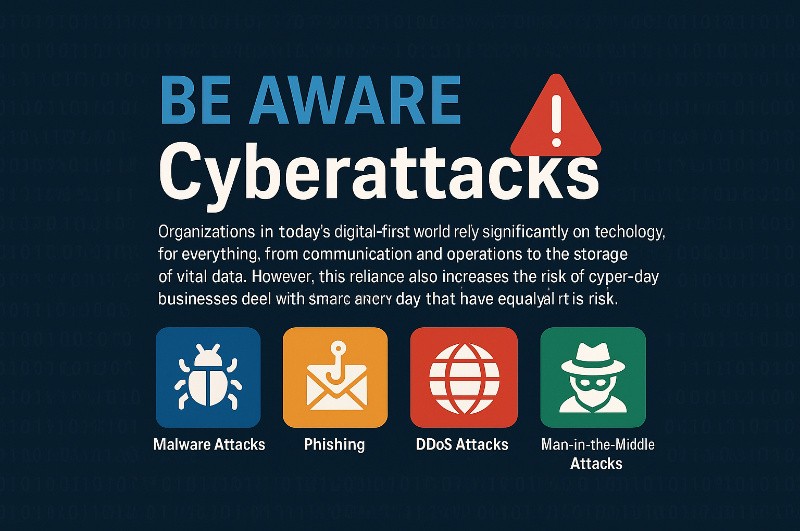
BEAWARE of Cyberattacks
Organizations in today’s digital-first world rely significantly on technology for everything,
from communication and operations to the storage of vital data. However, this reliance also
increases the risk of cyberattacks. Businesses deal with threats every day that have the
potential to cost them millions of dollars, disrupt services, or steal data. Furthermore, small
and medium-sized enterprises are equally at risk as large corporations.
So, what kinds of cyber attacks are out there you should be concerned? And why should
your organization care about cyber attacks? In this article, we’ll break down the most
common (and dangerous) types of cyber attacks, how they work, and why staying informed
is your best defense.
1. Malware Attacks
Let’s start with one of the most common threats: malware. Short for “malicious software”,
malware is any software designed to harm your devices, steal data, or gain unauthorized
access to your systems.
There are several types of malware:
Viruses: Like biological viruses, these attach themselves to files and spread when you open
them.
Worms: These can self-replicate and spread across networks without any user action.
Trojans: Disguised as harmless programs, they open the door for attackers once installed.
Ransomware: Locks or encrypts your data and demands payment to release it.
Spyware: Secretly monitors your activity and steals sensitive information.
Why it matters: A single malware infection can cripple your systems, shut down operations,
or leak customer data. In some ransomware cases, companies have lost millions or had to
rebuild their systems from scratch.
2. Phishing
Phishing is less about hacking your system and more about tricking your people. It’s a form
of social engineering, where attackers pose as trustworthy entities—like banks, colleagues,
or government agencies—to fool employees into clicking malicious links or sharing
confidential data.
Types of phishing include:
Email phishing: The classic “click this link” scam.
Spear phishing: Targeted at specific individuals (like HR or finance teams).
Whaling: Aimed at executives—think CEOs and CFOs.
Smishing and vishing: Delivered via SMS or phone calls.
Why it matters: Phishing is the starting point for many major breaches. All it takes is one
person to click a link or send login credentials for attackers to walk through your digital front
door.
3. DDoS Attacks (Distributed Denial of Service)
Ever tried visiting a website and it just wouldn’t load? It might be under a DDoS attack. In
these attacks, hackers flood a server with so much traffic that it crashes or becomes too
slow to use.
They do this using thousands of devices—often part of a botnet (a network of infected
computers). The result? Downtime, frustrated customers, and lost revenue.
Why it matters: Even a few hours of downtime can damage your reputation and cost you
business. E-commerce sites and financial services are frequent targets.
4. Man-in-the-Middle (MitM) Attacks
Imagine you’re having a private conversation, but someone is secretly listening in and
maybe even changing what’s being said. That’s a Man-in-the-Middle (MitM) attack.
These usually happen over unsecured networks (like public Wi-Fi), where attackers intercept
the data going between your device and a website or server. They might steal login
credentials, spy on communications, or redirect you to fake sites.
Why it matters: MitM attacks are hard to detect but can result in major data breaches,
especially if sensitive financial or customer information is stolen.
5. SQL Injection
SQL injection attacks target your databases—the places where sensitive data like customer
records, usernames, and passwords are stored.
An attacker finds a vulnerable form field (like a login box or search bar) and enters specially
crafted code instead of normal input. If your system isn’t properly protected, it will run that
code—allowing the attacker to view, delete, or manipulate data.
Why it matters: These attacks can expose large volumes of private information in seconds.
They’re especially dangerous for e-commerce sites and any platform with user data.
6. Zero-Day Exploits
A zero-day exploit refers to a security hole in software that the developers don’t even know
about—yet. Once attackers discover it, they move fast to exploit it before a patch is
released.
Because no fix exists when the attack happens, these are some of the most dangerous and
difficult-to-defend cyber threats.
Why it matters: Even the best software can have flaws. Zero-days are often used in high-
profile attacks against governments, banks, and critical infrastructure.
7. Credential Stuffing
We’re all guilty of reusing passwords. That’s why credential stuffing works so well. Attackers
use stolen username-password combinations (often from previous data breaches) and try
them on other sites.
Using automation tools, they can try millions of combinations in minutes.
Why it matters: Once they get into an account, they can steal data, make unauthorized
transactions, or impersonate users. If one employee uses the same password everywhere,
your entire system could be at risk.
8. Insider Threats
Not every attack comes from the outside. Insider threats happen when employees,
contractors, or partners misuse their access—intentionally or accidentally.
Sometimes it’s malicious (disgruntled employees stealing data). Other times, it’s just
careless behavior (sending sensitive files to the wrong email).
Why it matters: Insider attacks are harder to detect because the perpetrators already have
access. But the damage can be just as devastating.
9. Social Engineering
Social engineering tricks people into giving away confidential information by exploiting
human behavior—curiosity, fear, urgency, or trust.
Examples include:
Pretending to be IT support and asking for passwords.
Calling an employee claiming to be a vendor.
Physically tailgating someone into a secure office.
Why it matters: Technology can only protect you so much. If your people are fooled, no
firewall will save you. That’s why training and awareness are key.
10. Business Email Compromise (BEC)
This sophisticated form of email fraud targets companies that conduct wire transfers or
work with foreign suppliers. The attacker either spoofs or compromises a business
executive’s email account and then requests an urgent transfer of funds.
These emails look incredibly convincing and often bypass spam filters.
Why it matters: BEC scams have cost organizations billions. It’s one of the most financially
damaging cybercrimes around.
11. Drive-By Downloads
This type of attack doesn’t need you to click anything. Just visiting a compromised or
malicious website can trigger a drive-by download, silently installing malware on your
device.
Attackers often sneak these into advertising networks (called malvertising), making even
trusted sites risky.
Why it matters: These attacks are sneaky, fast, and don’t require any user interaction. If
your employees aren’t protected, even browsing online can be dangerous.
12. DNS Spoofing
Every time you type a website address, your computer uses the Domain Name System (DNS)
to find the right server. DNS spoofing tricks your system into thinking a fake website is real.
It’s like someone switching the signs on a road—you think you’re headed to your bank’s
website, but you end up on a fake version designed to steal your credentials.
Why it matters: DNS spoofing can lead to widespread phishing, credential theft, or malware
infections—all while looking totally legitimate.
13. Cross-Site Scripting (XSS)
In XSS attacks, hackers inject malicious scripts into websites that run in your browser. These
can be used to steal session cookies, deface websites, or redirect users to phishing pages.
It’s often found in forums, comment sections, or poorly secured input fields.
Why it matters: XSS can compromise users without them knowing, especially if your web
applications don’t sanitize inputs properly.
14. Supply Chain Attacks
In a supply chain attack, the attacker targets a third-party vendor that has access to your
systems—like software providers or IT service companies. If the vendor is compromised, so
are you.
A famous example is the SolarWinds breach, where attackers inserted malicious code into a
software update that affected thousands of customers.
Why it matters: You can have excellent cybersecurity, but if your vendors don’t, you’re still
at risk.
15. Cryptojacking
Cryptojacking involves secretly using your systems to mine cryptocurrency. It’s often done
through browser scripts or malware. While it might sound less dangerous, it slows down
systems, wastes energy, and often indicates deeper vulnerabilities.
Why it matters: Cryptojacking can be a sign that someone has already breached your
system. Plus, it drains resources and exposes security gaps.
Final Thoughts
Cyber attacks are evolving—and fast. As businesses move more operations online, the risks
grow. Understanding the different types of cyber threats is the first step in building a strong
defense.
No organization is too small or too secure to be a target. But with awareness, proactive
security measures, employee training, and regular testing, you can reduce your exposure
and protect what matters most.
Remember: Cybersecurity isn’t just an IT problem. It’s a business priority. [Talk to Us]
Author
-

Dinesh Mehn is the Founder and CEO of DigitoWork, specializing in IT Asset Management, IT Security, and cost optimization. A Certified Master Black Belt and former GE professional, he assists IT teams in enhancing efficiency and security. DigitoWork has been awarded the prestigious ISO 17025 certification for its IT Security Testing Lab, becoming the FIRST company in Telangana to achieve this milestone. This recognition reinforces DigitoWork's commitment to delivering IT Security Testing, Vulnerability Assessment & Penetration Testing (VAPT), Ethical Hacking, Red Team, Exploitation Testing solutions to organizations that need to improve Application Security Posture.