Honeypots: The Strategic Deception System for Modern Cyber Defense
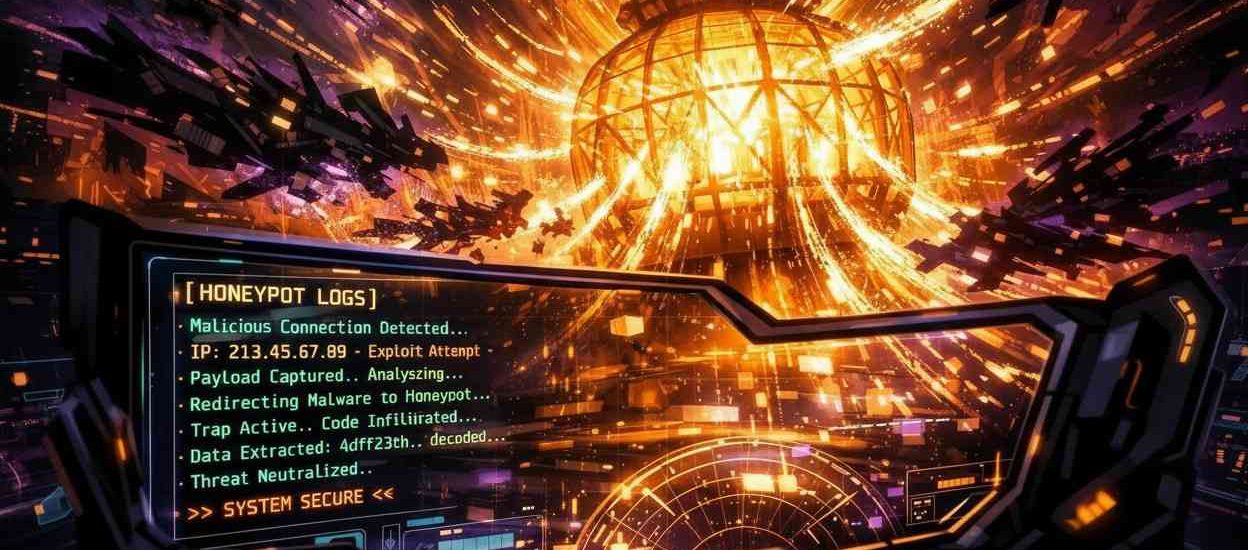
In the evolving theater of cybersecurity, a paradigm shift is occurring. Organizations are moving beyond purely defensive perimeters toward active deception—creating controlled environments designed to study, mislead, and frustrate attackers. At the heart of this strategy lies the honeypot: a deliberately vulnerable system that mimics legitimate assets to attract, detect, and analyze malicious activity.
Unlike traditional security measures that seek to block attacks outright, honeypots operate on the principle of strategic misdirection. They serve as digital tripwires, early warning systems, and intelligence-gathering tools, providing unique insights into attacker methodologies, tools, and intentions that firewalls and intrusion detection systems alone cannot offer.
Why Deception is Your Secret Weapon?
Traditional defenses work like a fortress wall—they try to keep everyone out. But skilled attackers will eventually find a weak spot. Honeypots operate differently. They create the illusion of weak spots on purpose, turning your network from a static target into an intelligent, observant environment.
The true power lies in what happens after an attacker takes the bait. Every keystroke, every uploaded tool, every attempted maneuver is captured and logged. This isn’t theoretical threat data from a report—it’s live, real-time intelligence about actual attacks happening right now against your decoy systems.
This intelligence becomes actionable in ways generic security alerts never can. When you see a new malware variant being deployed in your honeypot, you can immediately update defenses across your real systems. It’s cybersecurity clairvoyance—seeing attacks before they matter.
Building Your Deception Network
Start with Clear Objectives
Before deploying a single decoy, ask: what do you want to achieve? Early detection? Threat intelligence? Security team training? Your goals shape everything from honeypot complexity to placement.
- Low-interaction honeypots: Early warning systems that detect scanning.
- Medium-interaction honeypots: Capture malware payloads and scripts.
- High-interaction honeypots: Complete, isolated systems for deepest insights.
Strategic Placement is Everything
Place honeypots where attackers expect valuable targets:
- Near critical assets (as digital tripwires)
- In cloud environments (where visibility is limited)
- Within development and testing networks
- Among remote employee segments
The key is believability. Your honeypot should look, feel, and respond like a real system—complete with fake user data and simulated activity.
Integration Makes Intelligence Actionable
A honeypot working in isolation is like having a spy who never reports back. Connect your deception systems to existing security infrastructure:
- Feed alerts into your SIEM (Security Information and Event Management)
- Trigger workflows in your SOAR platform
- Share anonymized indicators with threat intelligence platforms
The Intelligence Goldmine: What You Learn
Real Tools from Real Attackers
- Capture live malware, custom scripts, and exploit frameworks with full context
- Understand toolchains and attack sequences
- Reveal attack playbooks that generic threat intelligence misses
Behavioral Patterns That Predict Moves
- Observe attacker tradecraft: speed, thoroughness, and operational security
- Map actions to frameworks like MITRE ATT&CK
- Recognize attack sequences in real network logs
Early Warning of Emerging Threats
- Detect zero-day exploits being tested against your decoys
- Gain days or weeks of lead time to patch real systems
- Get industry-specific insights on evolving threats
From Data to Defense: Making Intelligence Actionable
Automate Your Defenses
- Self-healing security: Automatically feed new attack signatures into IPS/IDS
- Continuous learning: Generate detection rules from observed patterns
- Proactive updates: Push malware hashes across defenses in real time
Sharpen Threat Hunting
- Move from random searches to targeted investigations
- Hunt for techniques seen in honeypots across production networks
- Turn isolated alerts into part of a known attack narrative
Train with Reality
- Use captured attack footage for realistic analyst training
- Demonstrate actual exploitation and lateral movement techniques
- Build practical recognition skills beyond theoretical knowledge
Guide Strategic Planning: Answer critical questions with evidence
- Where should we invest security resources
- Which vulnerabilities are being actively exploited?
- What attack vectors target our specific industry?
The Strategic Mindset Shift
Honeypots represent more than technology—they embody a fundamental shift in security philosophy. From passive defense to active observation. From hoping you don’t get hit to learning from every attempted hit. From generic threat reports to specific, actionable intelligence about attacks targeting your organization.
In today’s threat landscape, knowledge isn’t just power—it’s protection. Understanding your adversary better than they understand you creates asymmetric advantage that no firewall or antivirus can provide alone.
By welcoming attackers into controlled environments of your own design, you transform their attempts at compromise into your opportunities for learning. Every attack becomes a lesson. Every intruder becomes an unwilling teacher. And every piece of captured intelligence makes your real defenses stronger, smarter, and more resilient.
Author
-

Krishna Prasad is the Quality Manager at NABL IT Security’s ISO 17025-certified Security Testing Lab. He ensures that all security testing processes adhere to the highest quality standards and comply with global security regulations. With extensive experience in quality assurance, Krishna oversees the implementation of rigorous testing methodologies, guaranteeing that security assessments are both accurate and reliable.
Additionally, he manages asset tracking within the lab, ensuring that all security assets are effectively maintained, optimized, and up-to-date to support high-quality testing services. His dedication to quality and precision helps organizations enhance their security posture and meet compliance requirements in an increasingly complex cybersecurity landscape.